What is Python-Webkit?
Python-Webkit is a headless browser automation tool that wraps around the WebKit rendering engine via Python bindings. It allows developers and script authors to programmatically render web pages, interact with DOM elements, and capture visual or textual content — all without a graphical interface.
- It relies on the QtWebKit or GTK WebKit ports depending on the platform and installation
- It can be embedded into Python scripts to simulate browser behavior like clicking, form submission, and navigation
- It is often used in environments where newer headless solutions like Puppeteer or Playwright are unavailable or too resource-heavy
- It lacks compatibility with many modern JavaScript APIs and features due to reliance on outdated WebKit versions
Despite its limitations, Python-Webkit offers a lightweight option for headless automation tasks. However, its outdated engine can pose security and detection challenges, especially when repurposed for scraping or unauthorized interaction with web services.
What is Python-Webkit used for?
Python-Webkit is primarily used for automating web interactions through Python scripts. While it was originally developed for tasks like automated testing, crawling, and data extraction, it also finds niche applications in environments where modern headless frameworks are either unsupported or overkill.
- It is used for scraping websites where JavaScript rendering is required, but full browser emulation isn’t
- It enables DOM interaction for tasks like filling out forms, clicking buttons, and navigating paginated content
- It is sometimes used in legacy test automation frameworks or educational tools to demonstrate browser scripting
- In fraud contexts, it can be used for simple bot operations against websites with weak detection mechanisms
Due to its lack of support for modern features, it’s unlikely to be effective against modern SPAs or complex web apps. However, it can still pose a risk when used in scripted botnets or scraping networks targeting vulnerable endpoints.
How to detect Python-Webkit headless browser?
Python-Webkit exhibits several technical characteristics that can help defenders detect and block it in production environments:
- User-Agent strings may include identifiers for QtWebKit, GTK WebKit, or show outdated Safari/WebKit versions
- Many modern browser features are absent, such as
Intl,navigator.languages,deviceMemory, orWebGLRenderingContext - Canvas and SVG rendering tests often return artifacts or malformed results due to legacy rendering behavior
- TLS fingerprints may include deprecated cipher suites or lack modern extensions like ALPN or SNI
- JavaScript entropy is low — interaction timing, input patterns, and screen simulation lack natural variance
- Absence or default values in properties like
navigator.plugins,screen.colorDepth, orhardwareConcurrency
To block effectively:
- apply JavaScript environment tests to validate modern API presence and consistency
- flag sessions with legacy TLS handshakes or WebKit identifiers in the User-Agent
- introduce browser challenges that require modern rendering support (e.g., WebGL shaders, feature detection scripts)
- enforce progressive trust scoring based on environment fidelity and user interaction patterns
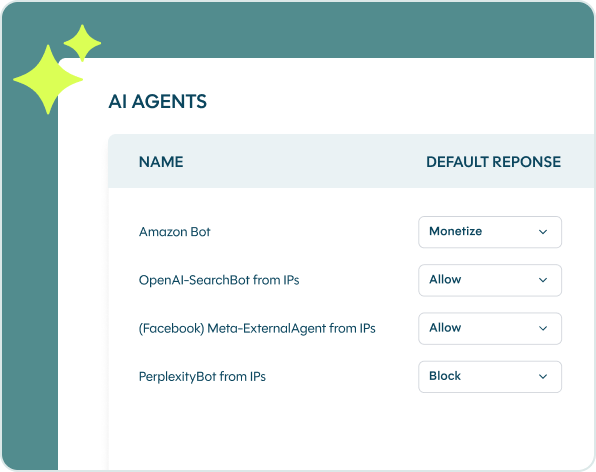
See which bots and AI agents bypass your defenses
Create your account to start analyzing and mitigating malicious bots and AI-drive threats in real-time