Cybersecurity & Data Protection—Key Differences & Benefits
Cybersecurity and data protection are words that people tend to use interchangeably. While they have similarities and often overlap, it’s kind of like discussing a rectangle and a square where both have four sides but are distinct shapes. In a digital world, your cybersecurity posture directly impacts your data protection and privacy initiatives.
Key Takeaways
- Distinct but Connected: Cybersecurity protects systems and networks from attacks, while data protection specifically focuses on the integrity, privacy, and availability of information.
- The Cost of Failure: With the global average cost of a data breach reaching $4.88 million in 2024, integrated protection is no longer optional.
- Compliance is Key: Privacy laws like GDPR and CCPA require organizations to secure user data against unauthorized access, making cybersecurity a legal necessity.
- Human Element: 68% of data breaches involve a human element, highlighting the need for solutions that don’t rely solely on user perfection.
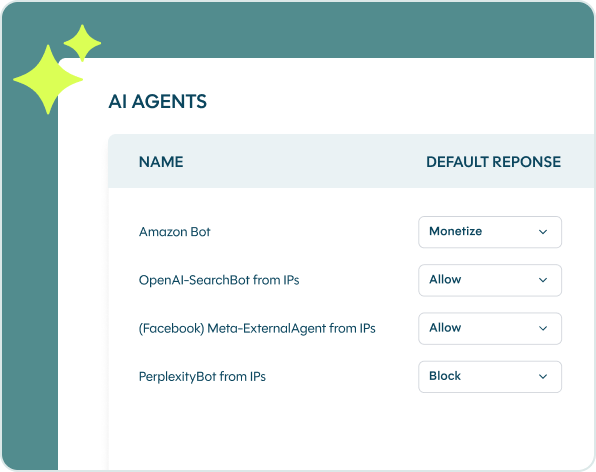
- Automated Protection: Real-time bot and agent trust management is essential to stop scraping, account takeover (ATO), and fraud without compromising user privacy.
Over the last few years, malicious actors have increased the number and speed of their attacks. According to IBM’s 2024 Cost of a Data Breach Report, the global average cost of a data breach has risen to $4.88 million. Furthermore, the 2024 Verizon Data Breach Investigations Report highlights that 68% of breaches involve a non-malicious human element, such as a person falling victim to a social engineering attack or making an error.
In short, you can experience a cybersecurity incident without necessarily experiencing a data breach.
Understanding the key differences between cybersecurity and data protection can help you better understand their unique benefits, especially when it comes to ensuring customer privacy.
What is the difference between data protection and cybersecurity?
Data protection is a subset of cybersecurity. While data protection focuses on ensuring data integrity, cybersecurity takes a broader approach by focusing on all the digital networks and systems that collect, transmit, process, and store information. While they complement each other, they also have distinctions that you need to understand.
What is cybersecurity?
Cybersecurity consists of the technologies, people, and processes that protect systems and networks. Usually, your cybersecurity program focuses on things like:
- Endpoint security: making sure devices are updated.
- Identity and Access Management (IAM): limiting access using a “need to know” approach.
- Network security: monitoring for abnormal activity on networks.
- Data security: protecting data from unauthorized changes.
- Application security: ensuring applications have security patches and can’t be used by cybercriminals.
Cybersecurity’s main objective is to keep unauthorized users from accessing data. Cyber attackers use various methods to gain unauthorized access so that they can steal data, also called data exfiltration.
What is data protection?
Data protection, also called data security, ensures data integrity and confidentiality by preventing unauthorized accidental or malicious changes to information. The important distinction here is that data protection includes accidental changes, like an employee who incorrectly inputs data.
Some typical data protection controls include:
- Encryption: scrambling data to make it unusable.
- Masking: hiding sensitive information from view.
- Erasure: deleting data so it can’t be found.
- Backup: making multiple copies so that you can revert to the correct data if something happens.
Why is privacy important in cybersecurity?
Privacy combines cybersecurity and data protection in a different way. Most privacy laws focus on the following:
- User control over data: rights to opt out, be forgotten, access, and rectification.
- Access: viewing and editing.
- Security: implementing technical controls to prevent cyber attacks.
Balancing robust security with user privacy is a critical challenge for modern enterprises. As Maciej Wlodarczyk, CISO of Sanoma Media Finland, notes regarding their choice of protection:
Cybersecurity implements access and security protections. However, it doesn’t respond to all the types of user rights covered by privacy laws. For a comprehensive cybersecurity and data privacy program, you need to have the technologies, people, and processes to achieve all three requirements.
Benefits of Combining Cybersecurity and Data Privacy
Privacy is a fundamental human right. Now that most organizations use digital tools, cybersecurity and data privacy are inextricably intertwined. When you create a holistic program encompassing both, you upgrade your cybersecurity while protecting consumers’ rights.
Prevent Data Breaches
It’s easy to think that only people outside your organization are a data breach risk. Most privacy laws extend that definition to employees who can view sensitive data, even when they don’t need to know it. For example, one of the first General Data Protection Regulation (GDPR) fines was the result of too many people having too much access. They didn’t even need to steal the data, just the ability to view it.
Stay GDPR Compliant
The GDPR was the first law with extraterritorial jurisdiction. It applies to any company, no matter where it’s located, that collects, transmits, or stores sensitive data owned by European citizens or residents. Additionally, you’re responsible for any vendors who process data on your behalf. This means you need to comply and you need compliant partners, like DataDome.
Build Customer Trust
Customers want to know that you protect them. People are afraid of having their data stolen because they fear identity theft. If your company suffers a data breach, then customers may take their business to your competitor.
Protect Revenue
Data breaches and privacy law violations cost money. When you combine enterprise cybersecurity with data privacy, you reduce costs arising from:
- Business interruption.
- System recovery.
- Customer notification.
- Fines.
- Lawsuits.
How to Protect Your Data Against Malicious Attacks
When you follow cybersecurity best practices and protect data privacy at the same time, you mitigate malicious attack risks.
Implement Multi-Factor Authentication
As part of an attack, many cybercriminals use stolen user credentials, like user ID and password. Multi-factor authentication (MFA) requires users to input additional information when they login, like a passcode sent to a smartphone or email address. Since the user needs to have their device with them, this provides another layer of confidence that they are who they say they are.
Limit User Access
When you limit user access according to the principle of least privilege, you grant only the access someone needs to complete their job function. By doing this, you mitigate privacy risks like accidentally viewing sensitive information even though they’re an authorized user.
Use a Botnet Detection Solution
Cybercriminals use botnets for various attacks, including DDoS and credential stuffing. A bot detection solution helps you mitigate risk by analyzing both technical and behavioral data to identify fraudulent traffic.
Continuously Monitor Security
As cybercriminals look for different ways to attack companies, the protections that you implemented may no longer be effective. You need to continuously monitor your devices, systems, and networks to ensure that everything is doing what you expect it to do.
Update Operating Systems and Software Quickly
Vulnerabilities are coding issues that create security weaknesses. Companies supply patches to fix them so that cybercriminals can’t use them during an attack. The sooner you install security updates, the more protected you are.
How DataDome Enhances Data Protection and Cybersecurity
Your business runs on sensitive information. You use consumer data across all areas of your business, from analytics to digital customer experiences. To protect your organization, you need a comprehensive cybersecurity and data protection program that mitigates risks.
Bot and agent trust management solutions continuously monitor your traffic to detect and mitigate risks before they can turn into a data breach. DataDome’s solution offers protection that outperforms, analyzing 5 trillion signals daily to stop attacks in under 2 milliseconds.
DataDome protects against cybercriminal activities like web reconnaissance, vulnerability scanning, and account takeover (ATO). By focusing on intent, not identity, DataDome ensures full compliance with privacy laws (GDPR, CCPA) while maintaining a false positive rate below 0.01%.
Frequently Asked Questions (FAQ)
No, effective data protection requires strong cybersecurity measures. While you can have cybersecurity without focusing specifically on data privacy, you cannot ensure data protection without the security infrastructure to defend it against breaches.
Automated bots are often used to scrape sensitive data or crack accounts (credential stuffing). A solution like DataDome blocks these malicious automated threats in real time, preventing data exfiltration and ensuring customer privacy is maintained.