What is Enterprise Cybersecurity?
Enterprise cybersecurity encompasses all practices, tools, and controls used to protect against cyberattacks. It safeguards data and vulnerable endpoints. Enterprise cybersecurity monitors data routes between devices, networks, and users.
Cyberattacks are becoming more sophisticated. Cyberattacks now also happen more often. 83% of businesses experience more than one data breach per year. Instances of cybercrime have increased by 72% in the last five years.
Enterprise cybersecurity solutions are also evolving. Modern enterprise cybersecurity software provides a solid defense against cyberattacks. Every business needs a robust enterprise cybersecurity solution.
Why is enterprise cybersecurity important?
Cyberattacks are a serious threat to businesses. Cyberattacks happen in every sector. Major multinational companies are always tempting targets. But small to medium businesses often have less stringent digital security measures. No matter what the size of the business, a cyberattack can be damaging.
How does cybercrime harm businesses?
Cyberattacks can have a range of negative impacts on a business. As well as financial losses, cyberattacks can disrupt operations. Data leaks can result in a loss of customer trust and weaken the reputation of a business.
Companies face costly recovery efforts after a cyberattack. Businesses suffer lost revenue and long-term reputational damage. Companies must also increase investments in cybersecurity measures to prevent future threats.
The impact of cybercrime on large organizations
A successful cyberattack can decimate the value of a large organization. The average cost of a successful cyberattack is approximately US $4.88 million.
SMBs are especially vulnerable to cyberattacks
Smaller businesses can also suffer major losses from cyberattacks. 43% of cyberattacks every year are against SMBs. A successful cyberattack causes an average loss of US $25,000 for SMBs. Only 14% of SMBs have the defenses to withstand a cyberattack.
What sectors do cybercriminals target?
Cybercrime will increase by 15% to reach a value of more than US $10.5 trillion within the next five years. Cyberattacks occur in all business sectors. But some industries are more vulnerable than others.
Healthcare cyber attacks are common. Healthcare companies store sensitive personal data, making them a prime target for cybercriminals. The healthcare cybersecurity market worldwide will be worth $35.3 billion by 2028.
The e-commerce industry is also targeted. The e-commerce industry loses an estimated $2.1 trillion every year to cyberattacks.
Other industries often targeted include financial services and the travel and hospitality industry.
All businesses have vulnerabilities. Business owners need robust cybersecurity and data protection measures.
Types of enterprise cybersecurity risks
Businesses face a range of cybersecurity risks from both internal and external sources. Cybercriminals are always searching for vulnerable companies with poor enterprise cybersecurity. Employees, customers, and third parties can also put corporate data at risk.
Business owners need to know how fraudsters commit cyber attacks. This knowledge can help you develop effective enterprise cybersecurity solutions. Some of the most damaging cyberattacks are due to:
Human error or negligence
Up to 95% of cybersecurity breaches occur because of human error. 68% of data breaches are the result of employee error or negligence. 15% of data breaches were due to an error or negligence by a third party, such as a contractor or supplier.
Employees or third parties can open up vulnerabilities in an organization’s cybersecurity. Employees often use weak passwords or make corporate data accessible to the public.
Phishing attacks
Cyberfraud uses social engineering techniques. Phishing is one of the most common methods of breaching enterprise cybersecurity measures. 36% of all data breaches are the result of a successful phishing attack.
In a phishing attack, a cybercriminal will pose as a legitimate source. They can then steal sensitive information. Phishing attacks are usually conducted via email. Phishing cyberattacks also involve fake websites. The aim is to trick victims into giving up sensitive data.
Ransomware attacks
Ransomware attacks occur when a user downloads malware. The malware encrypts data and locks out users from crucial systems. Cybercriminals will then demand a ransom payment in exchange for decrypting the data. 82% of recent ransomware attacks were against companies with 1,000 employees or less. 75% of SMBs reported that they could not continue operations after a ransomware attack.
Distributed Denial-of-Service (DDoS) attacks
A DDoS attack is when a botnet overwhelms a server or a network with traffic. This forces the server or network to go offline. DDoS attacks can disrupt crucial operations resulting in major financial losses.
Advanced Persistent Threats (APTs)
An APT is when unauthorized access to a system goes undetected. Cybercriminals can track and intercept communications and steal sensitive corporate data.
Configuration errors
Configuration errors in cloud-based infrastructure or on-premises systems provide entry vectors for cybercriminals. Misconfigured settings can lead to unauthorized access and data breaches. Configuration errors can also result in compliance violations. Incorrect privacy settings, for example, can breach international regulations such as the GDPR.
Vulnerable systems
Unfortunately, far too many businesses have insufficient enterprise cybersecurity measures in place. Lax cybersecurity provides hackers with an easy entry point. Cybercriminals can penetrate up to 93% of business security networks.
How to prevent enterprise cybersecurity attacks
Cybercriminals are refining their techniques. Cyberattacks are becoming more prevalent in all industry sectors. Despite this, you can defend your business using effective cybersecurity enterprise practices.
Assess system vulnerabilities and architecture
Reviewing your digital infrastructure and firewalls for vulnerabilities is crucial. Conduct quarterly penetration testing, information security audits, and vulnerability scans. High-risk businesses should have IT infrastructure and architecture reviewed on a monthly basis.
Define your enterprise cybersecurity needs
It’s important to understand your organization’s exact cybersecurity needs. Take into account how large your organization is. Consider what sector you operate in. Review how much sensitive personal and corporate data you deal with. Understanding these areas will enable you to develop effective enterprise cybersecurity solutions.
Educate employees on how to identify cybersecurity risks
Unfortunately, your people are a major cybersecurity risk. Train employees in the best enterprise cybersecurity practices. Your teams should learn good password management techniques. Teach employees to identify common cyberattacks such as malware or phishing attempts.
Use Multi-Factor Authentication (MFA)
Strict access management is critical to avoiding security breaches. Put in place multi-factor authentication (MFA) and restrict access to sensitive systems. By controlling who can access your systems, you make it harder for hackers to steal data.
Leveraging enterprise cybersecurity solutions
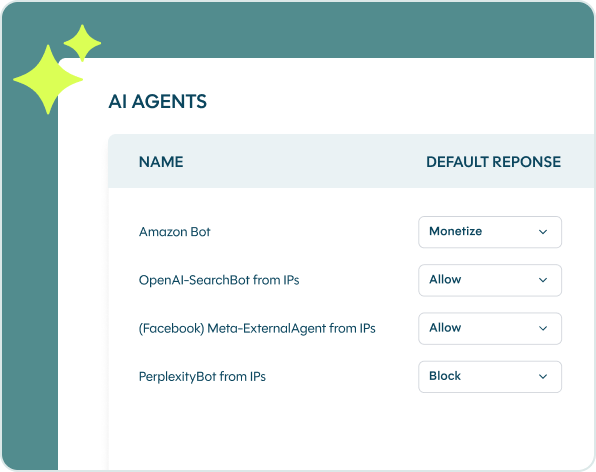
Neglecting enterprise cybersecurity can harm your business. The vast majority of cyberattacks come from automated scripts and bots. These malicious programs find and exploit weaknesses in websites, mobile apps, and APIs.
DataDome is a state-of-the-art threat detection software. DataDome stops cyber attackers before they reach their destination. DataDome provides you with real-time online fraud and bot detection. Our software can determine if a user should have access within two milliseconds.
Here’s how DataDome can assist you in developing robust protection against cyberattacks:
Cybersecurity monitoring
Continuous vigilance is important in the fight against cybercriminals. A network intrusion detection system (NIDS) can detect cyber threats in real time. NIDS cybersecurity systems analyze network traffic patterns for suspicious activities. The NIDS alerts admins to threats. Admins can then take appropriate action.
Security and compliance
Most countries have data protection frameworks. These frameworks protect the privacy and data of consumers. The best-known examples are the GDPR for the EU and EEA or the CCPA for California. Companies that breach these regulations face heavy penalties.
Ensure your company complies with all relevant legislation and regulations. Install a proven enterprise cybersecurity solution like DataDome.
Cloud security management
More businesses are moving away from on-premises software and data storage. But as Cloud computing becomes more popular, so too do the associated risks. According to Gartner, 82% of all cyberattacks involve cloud-stored data.
DataDome monitors your cloud security. Our software protects your outer layers from bot attacks.
Integrated security monitoring
Integrated security monitoring tools provide real-time visibility. They allow for the quicker identification of suspicious activity. DataDome lets you view the security measures for your complete tech stack.
Cyberfraud protection
Cybercriminals use automated bots to mimic human behavior and exploit vulnerabilities. DataDome offers you dependable cyberfraud protection. Our bot detection software prevents cyber fraud. DataDome identifies cyber threats and analyzes them in real time with 99.99% accuracy. Admins get notified of any cyber threats immediately.
Key takeaways
The rate of cyberattacks against organizations of every type is increasing. Cybercriminals use advanced software with powerful artificial intelligence and machine learning capabilities. Business owners must act to protect their enterprises, their employees, and their customers.
Your business needs a security strategy that works against all cyber threats. It is important to invest in robust enterprise cybersecurity. Your software must have the functionality to protect you against advanced, hard-hitting cyberattacks.
DataDome can safeguard your business against all forms of automated threats. With DataDome, you can upgrade the security posture of your business. Our software stays updated on the most current threat intelligence. Get a proven enterprise cybersecurity solution to ensure business continuity. Book a free online DataDome demonstration today.
FAQs
Enterprises face a wide range of cybersecurity issues. Criminals use social engineering techniques such as phishing to gain unauthorized access. Malware is often equipped to act as ransomware to hold systems hostage. Employees open the door to cybercriminals by maintaining poor digital security habits. Business owners need effective, in-depth cybersecurity strategies. It’s critical to ensure endpoint protection and guard vulnerabilities.
Phishing scams are the biggest cybersecurity threat today. The social engineering techniques used for phishing scams are low-cost. Phishing requires no technical knowledge. Criminals are often successful in gaining unauthorized access using phishing attacks. High success rates and low entry barriers ensure the popularity of phishing attacks.
Businesses are moving away from on-premises data storage and applications. Cloud-based computing and data storage solutions are more popular than ever. Moving to the cloud can put company data and customer data at risk. The move to the cloud has caused a rise in cybersecurity providers. Vulnerability management for cloud applications and cloud data security services are growing sectors.
Any business that stores sensitive personal data is a major target for cybercriminals. Healthcare, financial services, and the travel industry are often targets for cyberattacks.