What is Wendigo?
Wendigo is a high-level headless browser testing and automation framework built on top of Puppeteer and Jest. Originally developed by Bitnami (now part of VMware), it was designed to simplify end-to-end (E2E) testing of web applications by abstracting common UI interactions into readable, testable syntax.
At its core, Wendigo wraps Puppeteer, allowing developers to interact with Chromium-based browsers programmatically. It was primarily intended for developers automating UI testing, but its capabilities can be repurposed for headless bot operations and scraping.
Key Features
- Built on top of Puppeteer and Jest
- Simplified API for actions like clicking, typing, navigation
- Supports headless or full Chrome execution
- Useful for CI/CD and automated UI workflows
Advantages
- Easy integration into test pipelines
- Modular and extensible for various use cases
- Emulates full browser behavior
Disadvantages
- Inherits all Puppeteer-based fingerprinting weaknesses
- Last updates were years ago; project is now archived
- Often deployed with minimal anti-detection hardening
Despite its E2E testing origins, Wendigo can be abused for web scraping, price monitoring, and malicious automation if misused in fraud scenarios.
What is Wendigo used for?
Wendigo is primarily used for automated browser testing, but like many automation tools, it can be repurposed for malicious activity in fraud and bot ecosystems.
Legitimate Use Cases
- UI Testing: Automates web interfaces to simulate user actions (form submissions, clicks, navigation).
- Regression Testing: Ensures consistency in front-end behavior across deployments.
- Continuous Integration (CI): Easily integrates into pipelines for automated browser-based validation.
Malicious/Fraudulent Use Cases
- Scraping and Data Extraction: Wendigo can render JavaScript-heavy pages, simulating full browser interactions to bypass content protection layers.
- Automated Browsing for Click Fraud: Bots can mimic engagement (clicks, scrolls, dwell time) using Wendigo scripts.
- Credential Stuffing / Fake Form Submissions: Attackers may leverage its automation to test credential lists or submit forms at scale.
Although Wendigo is not as popular as Puppeteer or Playwright today, it still appears in bot frameworks due to its scriptability, headless operation, and legacy integrations in older fraud scripts.
How to detect Wendigo headless browser?
Puppeteer Fingerprint Leakage
Wendigo uses Puppeteer under the hood. Detect common artifacts:
navigator.webdriver === true
Missing navigator.plugins, navigator.languages, navigator.permissions.query() anomalies
window.chrome object is undefined or partial
Default Viewport & Screen Resolution
Many Wendigo deployments use default headless viewport sizes (e.g., 800×600). Check for non-human-like resolutions or full-screen mismatches.
Behavioral Inconsistencies
Actions are executed too quickly (clicks, scrolls, typing) without the natural delays seen in human interaction. Use honeypots or time-based challenges.
JS Feature Discrepancies
Mismatch between reported User-Agent (claims full Chrome) and missing modern JS APIs (e.g., WebGL, AudioContext).
Static TLS/JA3 Fingerprinting
Connections from Wendigo often use standard TLS stacks (especially in headless environments) with repeatable JA3 hashes.
Absence of Real Input Events
Tools like Wendigo may simulate DOM events directly (e.g., .click() instead of real mouse input). Monitor for absence of pointer or touch events in expected contexts.
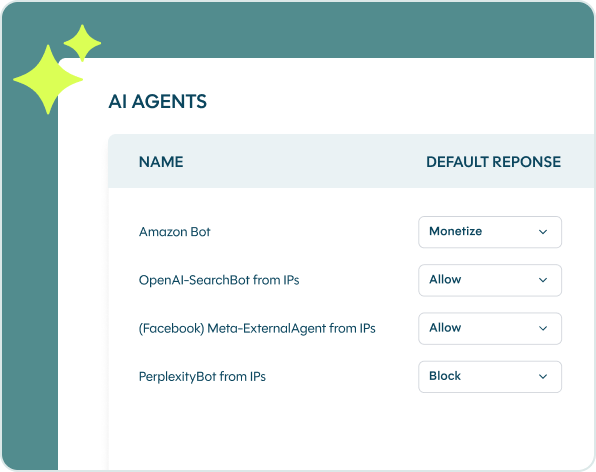
See which bots and AI agents bypass your defenses
Create your account to start analyzing and mitigating malicious bots and AI-drive threats in real-time