How to prevent a carding attack.
Carding is a cybersecurity threat where a malicious actor tries out a credit, debit, or gift card number against your payment gateways to test the number’s validity. The actor wants to figure out the missing values in the card number, so they can either resell the updated information or buy goods with the stolen payment data.
Carding is a growing problem for any company that sells goods or services online. Juniper Research estimated that retailers are set to lose $130 billion in card-not-present (CNP) fraud by 2023. CNP transactions are a major source of card fraud, because the card isn’t protected by chip-and-PIN and the merchant cannot physically verify the cardholder’s identity.
This is the first in a series of articles that will explain what you can do to prevent a carding attack, what to do when you’re under a carding attack, and what steps you can take to recover from a carding attack.
3 Steps to Prevent a Carding Attack
Although carding attacks are a growing problem, it’s not all bad news; there are steps you can take to prevent these attacks and protect your business.
- Make sure your payment gateways use the Address Verification System (AVS) and Credit Verification Value (CVV) matching. AVS checks if the billing address of your customer’s account matches the one on the card. CVV checks for the three- or four-digit number on the back of the card. Both make card fraud significantly harder.
- Use HTTPS and a signed SSL/TLS certificate to authenticate, encrypt and decrypt data securely. These protocols are crucial for online transactions and most modern browsers will flag their users when a website doesn’t have them or hasn’t set them up properly. Such websites are most vulnerable to carding attacks.
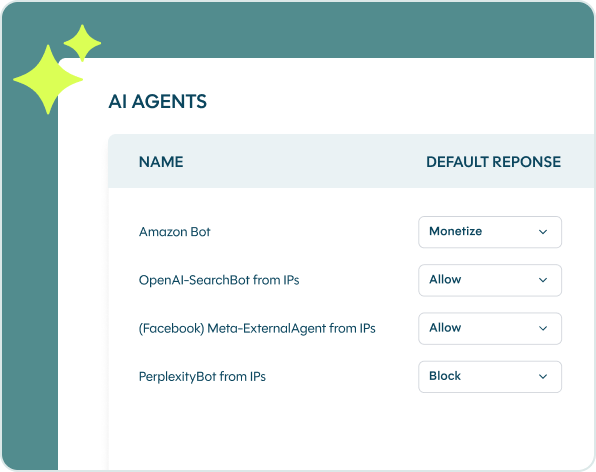
- Remember that carding attacks are automated threats and as such, you need a robust online fraud and bot management solution in place. After all, fraudsters don’t manually try to figure out missing card details; they use scripts to do so automatically. That’s why the right bot protection solution is crucial in the fight against carding, for several reasons:
-
- It can detect an automated threat not just at the point of transaction, but from the moment it enters your website, stopping the threat well before it turns into a fraudulent transaction.
- It checks every request for browser fingerprints, IP quality, mouse behavior, HTTP headers, mobile fingerprints, and many other variables. If the solution is still uncertain whether a request is a threat or not, it will serve up an additional authentication measure, such as a Captcha.
- It monitors unusual activities, such as requests coming from countries you don’t do business in, hundreds of login attempts on one account, or the exact same device used by different customers. It then either challenges or blocks those requests.
In Conclusion
Carding attacks are how most cybercriminals commit CNP fraud. Because carding is almost exclusively an automated threat, you can protect your mobile apps and websites with the right bot protection solution. DataDome is an automated fraud prevention tool that stops all carding attacks, as well as other automated attacks that are often tied to carding, such as credential stuffing and account takeovers.