What Is Bot Management & Why Your Business Needs It in 2026
Your website is under attack, and you’re likely exposed. According to DataDome’s 2025 Global Bot Security Report, 61% of websites are unprotected against simple bot attacks, and less than 3% of websites are fully protected.
This is why bot and agent trust management is so crucial for any online business. With sophisticated bots now using AI and advanced fingerprinting evasion techniques to mimic human behavior, investing in robust bot and agent trust management software is a necessity.
In this article, we’ll explore why bot management is so important in the AI era, and how a robust bot and agent trust management solution can help you protect your website, mobile apps, and APIs from cyberfraud.
Key takeaways
- Bot management is about smart differentiation, not blanket blocking. The goal is to distinguish between beneficial bots that help your business and malicious bots that cause harm, by letting the good through while stopping the bad ones.
- Modern bots are sophisticated adversaries that mimic human behavior. Today’s malicious bots use machine learning and advanced techniques like nonlinear mouse movements and randomized clicks to evade detection, making traditional security measures ineffective.
- Scalable attacks require scalable defenses. Since bots attack in massive volumes with hundreds or thousands operating simultaneously, manual detection and response is impossible. Automated, real-time protection is essential.
- Bot attacks go far beyond simple scraping. Malicious bots orchestrate complex schemes, including account takeovers, credential stuffing, inventory scalping, fake account creation, and targeted DDoS attacks that can devastate businesses financially and reputationally.
- Effective bot management uses multiple response strategies. Instead of just blocking suspicious traffic, advanced solutions use techniques like traffic throttling, content misdirection, and honeypots to control bot behavior while minimizing false positives that could block legitimate users.
What is bot management?
Bot management is the practice of identifying each individual bot on your network, understanding its intent, and responding appropriately based on whether it’s trustworthy.
Useful bots, like SEO tools or Googlebot and Bingbot, should be allowed to access your website so that you rank in search engine results. Similarly, trusted AI agents—like verified shopping assistants—should be enabled for frictionless agentic commerce.
Malicious bots, such as those that intend to steal your content or prevent your real users from accessing your website, should be blocked immediately. Bot management involves both detecting bot activity and determining its intent, be it malicious or not.
There are two key challenges in bot management:
- Differentiating between legitimate human traffic, AI agent traffic, and bot traffic
- Differentiating bots with good intentions (good bots) vs. those with malicious intentions (bad bots)
Today’s malicious bots and AI agents are extremely sophisticated, which makes bot detection challenging. They can mimic human behaviors, which makes differentiating between human users and bots is very challenging without the right bot management solutions.
And remember, not all bots are bad. There are good bots that can be beneficial for your site. For example, Googlebot crawls websites and indexes them so people can find them on Google. If you want your site to be featured on Google, then you shouldn’t block Googlebot—but you should block bad bots when they appear.
So, a proper bot management practice consists of two things:
- Efficient detection of bad bot traffic
- Control/mitigation of hostile bot traffic
How does bot management work?
One of the two key challenges in bot management is differentiating between legitimate human traffic and bot traffic. When a bot manager incorrectly blocks human visitors, we call it a false positive.
When a bot manager thinks you’re a bot
On the other hand, if we are too afraid about false positives, there is also an increased risk of letting too many bots in, causing false negatives instead.
Today’s malicious bots have become very apt at mimicking human behaviors. Bots can now use machine learning technologies to intelligently create seemingly random human behaviors like clicks and keystrokes. A bot manager and agent trust manager that uses intent-based detection powered by AI models is now necessary to counter sophisticated threats.
A common approach used by many bot management software providers is to show a CAPTCHA to users suspected of being bots, so they have to verify that they are human.
However, traditional CAPTCHAs are no longer very effective, especially with the popularity of CAPTCHA farm services, which include human users solving traditional CAPTCHAs before passing the connection to malicious bots.
To prevent both false positives and false negatives, your bot management solution should be able to:
- Handle feedback using a real-time feedback loop to mitigate sudden changes in behavior
- Effectively identify anomalies and adjust the mitigation accordingly
- Dynamically adapt to new patterns in real-time via iterative machine learning (ML)
- Use both fingerprinting (browser, OS, version, etc.) and behavioral analysis to distinguish between humans and bots
3 reasons why bot management is business critical
Bots are best used at scale. If you detect one, chances are that hundreds or even thousands have slipped through the net. Human-powered, manual bot mitigation does not stand a chance against large bot attacks. They have to be met with automated, scalable defenses.
In general, there are three core advantages of having a proper bot management solution:
1. Real-time detection and identification of bot activities
Real-time detection is a crucial component of effective bot management systems to ensure bot threats are blocked before they can negatively impact your business. Unchecked, malicious automation can be used to launch DDoS attacks, phishing attacks, and more.
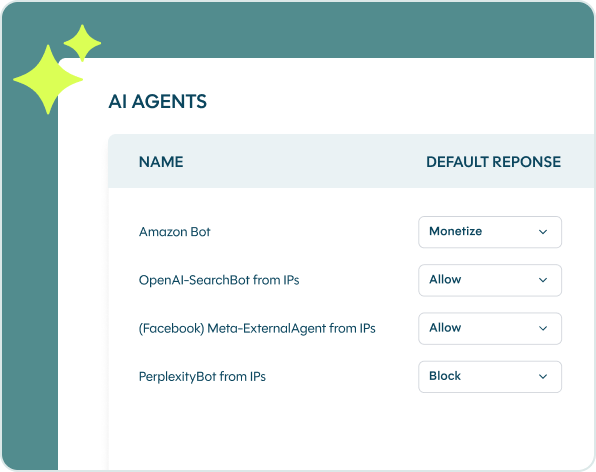
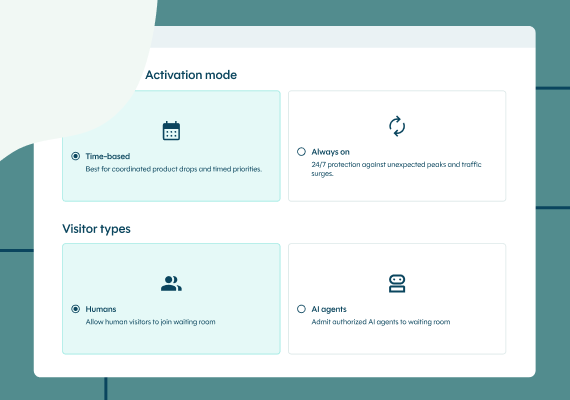
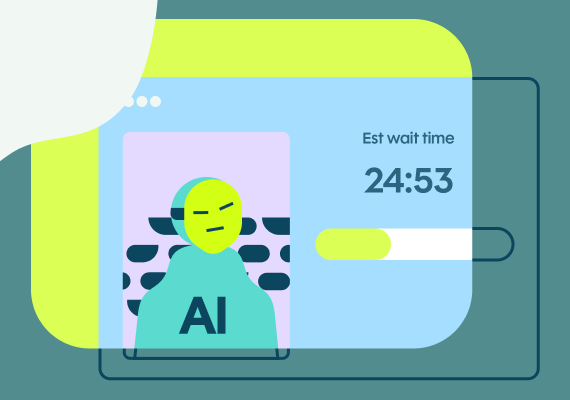
Modern bot management solutions include Agent Trust capabilities to help you differentiate between good bots, trusted AI agents, and malicious bots or AI agents. This allows you to stop unwanted bot traffic at the edge, while also reaping the benefits from good bots and agents, like agentic commerce.
2. To mitigate the negative impact of bots on website performance
Not all non-human traffic is useful for your website, so proper bot management is also necessary to prevent resource waste.
LLM crawler traffic quadrupled across DataDome’s customer base in 2025, underscoring the importance of retaining control over which crawlers can access your content and data. The last thing you want is to overload servers with bot traffic during a peak traffic period and slow down site performance for real customers.
3. To control malicious bot activity
Last but not least, a bot manager should control malicious bot activities. Bad bots can cause severe negative impacts on your business. They can:
- Scrape and steal your content
- Conduct scalping attacks
- Launch credential stuffing
- Orchestrate brute force attacks
- Launch a full-scale DDoS attack
Static rules don’t work against these attacks. Good bot detection software should provide attack responses that are optimized for each different kind of threat.
What is the difference between good bots and bad bots?
Good bots and bad bots differ primarily in their intent and impact on websites and users.
Good bots perform beneficial functions like search engine crawling, website monitoring, price comparison, and customer service chatbots. They typically follow the policies set in your robots.txt file, operate transparently, and help businesses by improving search visibility and user experience.
Bad bots, on the other hand, are designed for malicious purposes such as data scraping, credential stuffing, account takeovers, inventory hoarding, fake account creation, and DDoS attacks. They actively try to evade detection, mimic human behavior to bypass security measures, and can cause significant harm including revenue loss, data breaches, infrastructure overload, and damaged user experiences.
While good bots should be allowed and even encouraged to access your site, bad bots need to be met with good bot protection.
How can bad bots harm your business?
Before you learn how to stop bot attacks, it’s important to understand the risks they present. Bot detection relies upon understanding a bot’s intention, which is usually one of the following.
Scraping
Scraper bots target your websites, apps, and APIs to extract valuable data from them that will then be used for harmful purposes. Scraping can target your prices, products, content, and anything else that’s publicly available.
Some scrapers are okay (in which case, they are typically called “crawlers”), such as Googlebot and partner bots, but most scrapers worsen performance and drain your resources.
Scalping
Scalper bots take the joy out of online shopping. They buy or hold new limited-edition products in seconds, ruining product launches and real customers’ experiences. Scalper bots are also known as shopping bots, purchasing bots, or sneaker bots.

Highly anticipated sneakers like these Air Jordan 1 High “Travis Scott” are a popular target for sneaker bots
Popular product categories for scalping are concert tickets, sneakers, or hyped products such as a new graphics card or console. But any limited-edition product with a reasonably high retail price is up for grabs.
Account takeover (ATO)
Account takeover fraud happens when malicious bots gain access to online accounts. The attackers then use valuable information in those accounts to commit identity fraud, payment fraud, or to simply sell it all on the bootleg market.
Because the customer sits right in the middle of an ATO attack, it reflects poorly on your company’s reputation and should be avoided at all costs. A single ATO can break the customer trust you’ve spent years building up.
Credential stuffing
One of the ways hackers gain access to online accounts is through credential stuffing. Credential stuffing bots use databases of stolen login and password combinations to try and gain access to user accounts.
If they succeed, it’s an account takeover that can have serious, costly consequences. But even if they don’t succeed, credential stuffing bots are a big drain on your website’s infrastructure, and can even take your website offline.
And because people often use the same username and password for multiple websites, one compromised account can lead to severe consequences across multiple sites.
Brute force
Brute force attacks happen when hackers send automated bots to run through a large number of solutions to a problem. The most common brute-force attack is a password-guesser: A bot that will run through millions of combinations trying to access password-protected information.
The firepower of these bots means they can test a large number of combinations in a very short time. This, too, will drain your website’s infrastructure and could possibly lead to the exposure of confidential information.
Fake account creation
Some bots need to create fake customer accounts to do their job. For example, shopping bots will often create several fake accounts to snatch multiple of the same product at once. These types of bots enter via your registration page and will lead to a large number of seemingly empty user accounts in your user databases.
These fake accounts aren’t just used to scoop up products automatically. They can go on to influence product reviews, distribute false information, and spread malware. It’s in your best interests to remove fake accounts without impacting the ability for a user to register on your website or app.
DDoS attacks
A DDoS attack will use botnets to try and overwhelm your server or network until it either slows down significantly or crashes. The intent is to make your product and services unavailable to your users.
Some botnets do this by flocking in to your website, mobile app, or APIs in large numbers (a volumetric attack), while other DDoS attacks are more specific and target one particular aspect of an application or server (such as the WordPress endpoint of your WordPress websites).
DataDome recently stopped a 2.45-billion-request DDoS attack against a high-traffic content platform. This 5-hour attack failed to trigger traditional rate limits, illustrating how traditional defenses are no match for sophisticated attacks.
Managing bots and AI agents with DataDome
The right bot management approach is no longer about simply blocking all traffic coming from bots. It’s about leveraging both identity and intent to let good automation in and keep the bad out.
DataDome’s bot and agent trust management solution helps you do just that. With 5 trillion signals analyzed daily across more than 85,000 AI models, DataDome stops bot attacks in less than 2ms.
Book a demo today to learn more about DataDome, or run a free Vulnerability Scan of your website to test your current bot defenses.
Bot management FAQ
A bot manager protects your websites, mobile apps, and APIs from undesired or malicious bot traffic by blocking their access. It does so while letting through bots that you’ve added to your allow list, as well as good bots like Googlebot. The right bot manager will free up your IT resources while protecting you against harmful online attacks.
Bot management works by analyzing various signals from incoming traffic including IP reputation, behavioral patterns, device fingerprints, and request characteristics. Machine learning algorithms process this data in real-time to distinguish between humans, good bots, and bad bots, then apply appropriate security measures.
Bot protection solutions are essential because manual detection is impossible at scale, sophisticated bots can mimic human behavior, and the volume of bot attacks continues to grow. Without proper protection, organizations face risks including data breaches, revenue loss, infrastructure overload, and compromised user experiences.
Yes, modern bot management solutions like DataDome provide comprehensive API access for integration with existing security infrastructure. APIs allow developers to customize bot detection rules, access real-time threat intelligence, and integrate bot protection directly into applications and websites.
Essential features include real-time detection and blocking, behavioral analysis capabilities, machine learning-powered classification, comprehensive reporting and analytics, API protection, low false positive rates, easy integration options, and 24/7 monitoring. Look for solutions that can distinguish between good and bad bots with high accuracy.