How to Prevent Layer 7 DDoS & Application Layer Attacks
Layer 7 DDoS protection is a specialized security measure that defends web applications against sophisticated attacks targeting the application layer of the OSI model. Unlike traditional DDoS protection that focuses on network bandwidth, L7 protection specifically guards against attacks that mimic legitimate user behavior, such as HTTP floods, DNS query attacks, and malicious API requests.
TL;DR
- Layer 7 DDoS attacks target the application layer (HTTP, DNS, APIs) and are harder to detect than network-level attacks because they mimic legitimate user behavior
- 56% of DDoS attacks on AWS in 2023 were sophisticated L7 attacks, with the first half of 2024 seeing a 200% increase in DDoS attack size
- Average costs: Organizations face $6,000 per minute during attacks, with global data breach costs reaching $4.88 million in 2024
- Attack volume surge: 512,000 DDoS attacks occurred in Q4 2024 alone, up from 274,000 in Q1 2023—an 87% increase
- Key attack types include HTTP floods, Slowloris attacks, DNS query floods, and WebSocket connection floods
- DataDomeblocks L7 DDoS attacks in under 2 milliseconds with a false positive rate below 0.01%, analyzing trillions of signals daily with autonomous, always-on protection
In this article, we’ll explore the mechanics of Layer 7 DDoS attacks and the various types of L7 attacks. Most importantly, we’ll discuss modern protection strategies and cost considerations to help organizations defend against these evolving threats. Whether you’re a security professional, business leader, or IT administrator, this article will provide you with essential insights into L7 DDoS protection.
The scale of the threat is unprecedented. According to Statista, DDoS attacks worldwide surged from 274,000 incidents in Q1 2023 to 512,000 in Q4 2024: an 87% increase in less than two years. Meanwhile, Forrester’s 2025 Cybersecurity Predictions report warns that cybercrime is expected to cost businesses $12 trillion in 2025, with DDoS-for-hire services becoming increasingly sophisticated and accessible to threat actors.
What is a Layer 7 DDoS attack?
An L7 distributed denial of service (DDoS) attack targets the application layer of the OSI model, where common internet protocols like HTTP operate. Unlike network-layer DDoS attacks, L7 attacks are more sophisticated and can be devastatingly effective with relatively low amounts of bandwidth. These attacks are typically executed with a botnet. They specifically target the layer where web browsers and web applications communicate, making them dangerous for businesses that rely heavily on web-based services.
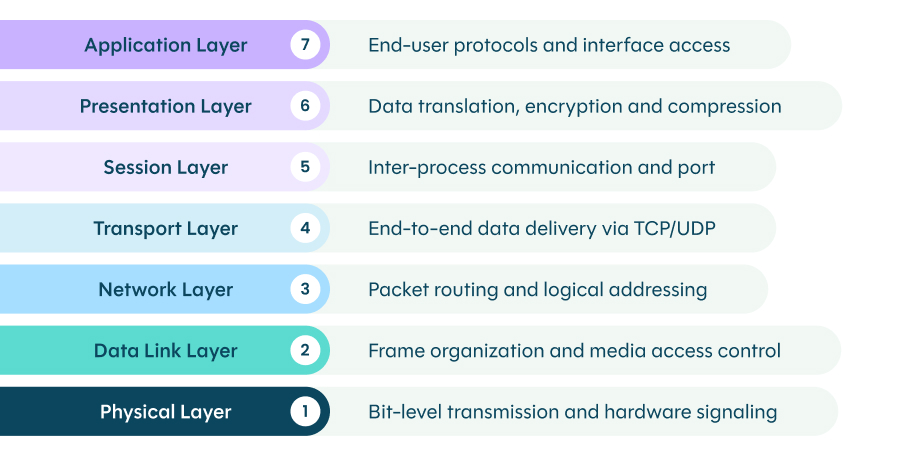
Layer 7 is the top layer of the OSI model
L7 attacks can vary significantly in their approach, from high-volume HTTP floods to “low and slow” tactics that gradually exhaust resources. What makes them particularly dangerous is their ability to mimic legitimate user behavior, allowing them to bypass traditional defense mechanisms that focus solely on traffic volume. Whether through massive request floods or subtle connections, L7 DDoS attacks can effectively overwhelm application resources and disrupt services.
Common types of Layer 7 DDoS attacks
| Attack Type | Bandwidth Required | Detection Difficulty | Primary Target | Impact Speed |
|---|---|---|---|---|
| HTTP Flood | High | Medium | Web servers, APIs | Fast (minutes) |
| Slowloris | Very Low | High | Web server connections | Slow (hours) |
| DNS Query Flood | Medium | Medium | DNS infrastructure | Fast (minutes) |
| WebSocket Flood | Low | High | Real-time applications | Medium (30+ min) |
HTTP flood attacks
The most common form of L7 DDoS attacks, HTTP floods overwhelm servers by sending a massive volume of seemingly legitimate HTTP GET or POST requests. This type of attack targets resource-intensive elements of web applications, such as:
- Search functionality that requires database queries
- Login pages that need credential verification
- Shopping cart systems that process transactions
- Form submissions that trigger backend processes
What makes a HTTP flood particularly dangerous is its ability to consume both network bandwidth and server CPU/memory resources. For example, a single POST request to a checkout page can require multiple database operations, session handling, and payment processing verification. All are resource-intensive tasks that can quickly overwhelm servers when multiplied across thousands of malicious requests.
Slowloris attacks
Named after the slow-moving primate, Slowloris attacks exemplify the “low and slow” approach to DDoS. These attacks maintain connections to the target web server by:
- Opening multiple connections to the target server
- Sending partial HTTP requests at a very slow rate
- Periodically sending subsequent HTTP headers, but never completing the request
- Keeping connections open for as long as possible
The strength of a Slowloris attack lies in its efficiency: It requires minimal bandwidth while creating maximum impact. When enough connections are established, the server’s maximum concurrent connection pool becomes exhausted, preventing legitimate users from connecting. Many web servers are configured with timeouts too long to effectively mitigate these attacks.
DNS query flood attacks
While technically targeting the DNS layer, a DNS query flood attack manifests at the application layer by overwhelming DNS servers with queries. Attackers typically employ two main strategies:
- Random subdomain attacks that generate unique, non-existent domain lookups
- Legitimate domain queries at high volumes that overload DNS resolvers
The impact extends beyond just DNS servers. When DNS services fail, all dependent applications and services become unreachable, creating a cascading effect of service disruption. Many organizations underestimate the resources required for DNS infrastructure, making this attack vector particularly effective.
WebSocket connection floods
A more modern attack vector that targets real-time web applications, WebSocket floods exploit the persistent nature of WebSocket connections. These attacks:
- Establish numerous WebSocket connections simultaneously
- Keep connections open indefinitely
- Send minimal data to maintain connection activity
- Target applications requiring real-time updates (e.g. chat systems, gaming servers)
Unlike traditional HTTP connections that close after each request/response cycle, WebSocket connections remain open, making them an attractive target for attackers. A successful WebSocket flood can exhaust server memory and connection handling capabilities, leading to degraded service for legitimate users or even complete system failure.
The real cost of L7 DDoS attacks
The financial impact of L7 DDoS attacks is substantial. As of 2024, organizations face average costs of approximately $6,000 per minute during an attack(3). The first half of 2024 saw a 200% increase in DDoS attack size compared to the previous year(3), indicating that these attacks are becoming more powerful and costly to mitigate.
Immediate financial consequences
During an active DDoS attack, organizations face severe immediate financial impacts that go beyond lost sales. E-commerce sites can lose thousands in revenue per minute of downtime, while also incurring costs from failed transactions and incomplete payments that may never be recovered. Companies often face unexpected expenses from emergency response staffing and resource allocation, compounded by potential bandwidth overage charges from their hosting providers due to the massive spike in malicious traffic.
Business reputation damage
The reputational impact of DDoS attacks can be devastating, with studies showing that 66% of consumers would not return to a website after a data breach(4). This loss of customer trust often leads to long-term brand damage, as negative publicity spreads rapidly across social media platforms. During extended service disruptions, competitors may gain significant market share advantage, creating lasting effects on business performance.
Operational impact
DDoS attacks create significant operational disruptions that affect the entire organization. IT teams must be diverted from their regular duties to handle the attack, while systems restoration and data verification processes consume valuable time and resources after the attack subsides. The strain on infrastructure during attacks can lead to accelerated hardware wear, while critical business processes and service delivery face potentially costly delays.
Regulatory and compliance issues
Organizations face mounting regulatory pressures following DDoS attacks, often incurring expenses related to breach notifications and legal counsel. Service disruptions may violate regulatory requirements, leading to potential fines and the need for additional compliance checks and documentation. These incidents frequently result in increased cybersecurity insurance premiums, adding to the long-term financial burden.
Organizations implementing specialized Layer 7 DDoS protection see immediate operational benefits:
4 Proven DDoS protection strategies
As cybersecurity expert Chuck Brooks notes in Forbes, “DDoS as a service platforms are used by criminals to launch assaults against corporate websites and demand ransom payments, threatening to degrade the service if the money is not paid.” This evolution in attack methods necessitates equally sophisticated defense strategies that go beyond traditional network-level protections.
Defending against L7 DDoS attacks requires a sophisticated, multi-layered approach that combines multiple technologies and methodologies. Here’s a detailed look at DDoS mitigation strategies:
Advanced traffic analysis
Modern Web Application and API Protection (WAAP) solutions represent the evolution of traditional WAF technology, incorporating multiple advanced detection techniques:
Behavioral analysis
- Establishes baseline patterns for normal user behavior
- Monitors metrics like request rates, session patterns, and resource usage
- Identifies anomalies that deviate from established baselines
- Uses machine learning to adapt to changing traffic patterns
Request fingerprinting
- Analyzes HTTP headers, cookies, and client characteristics
- Identifies bot signatures and automation tools
- Maintains databases of known good and bad fingerprints
- Updates fingerprint databases in real-time based on new threat intelligence
Rate limiting and throttling
- Implements intelligent rate limiting based on multiple factors
- Adjusts thresholds dynamically based on traffic patterns
- Applies different rules for different endpoints and user types
- Uses token bucket algorithms for precise traffic control
Real-time threat intelligence
Modern protection systems leverage vast networks of threat intelligence to create a proactive defense against emerging attacks. Through collaborative defense networks, these systems share threat data across protected sites in real-time, enabling rapid identification and blocking of known malicious IP addresses while detecting new attack patterns as they emerge.
Advanced machine learning systems process billions of requests to identify both known and new attack patterns, using both supervised learning for recognized threats and unsupervised learning to detect previously unknown attack types.
These systems continuously update their detection models based on new data, while automated response systems implement immediate protective measures when threats are detected. The system’s ability to scale defenses automatically based on attack volume, coupled with detailed analytics and reporting, provides organizations with comprehensive DDoS mitigation that evolves alongside new threats.
Geographic traffic management
Modern geographic protection goes far beyond simple geoblocking:
Advanced geolocation analysis
- Uses multiple data points to verify traffic origin
- Identifies traffic from residential vs. datacenter IPs
- Detects proxy and VPN usage
- Maintains databases of legitimate vs. suspicious IP ranges
Regional traffic patterns
- Establishes normal traffic patterns for different regions
- Identifies suspicious regional traffic spikes
- Applies region-specific protection rules
- Adapts to legitimate regional traffic changes
Dynamic traffic routing
- Routes traffic through regional scrubbing centers
- Implements anycast network architecture
- Provides automatic failover capabilities
- Optimizes routing for both security and performance
Zero-day attack prevention
With attackers now weaponizing vulnerabilities in as little as 22 minutes after proof-of-concept publication(5), protection systems must operate at unprecedented speeds to prevent zero-day attacks. Adaptive rule systems form the foundation of this protection, automatically updating security rules based on new threats and implementing virtual patching for newly discovered vulnerabilities before official patches become available.
These systems are powered by sophisticated AI analysis that uses deep learning to identify attack patterns and analyze traffic characteristics in real-time. That’s how it detects the subtle indicators of new attack types before they can cause significant damage. Continuous proactive monitoring scans for system vulnerabilities while tracking emerging threats and attack trends on the dark web, to provide early warning of potential attacks so organizations can strengthen their defenses before attacks materialize.
How DataDome protects against Layer 7 DDoS attacks
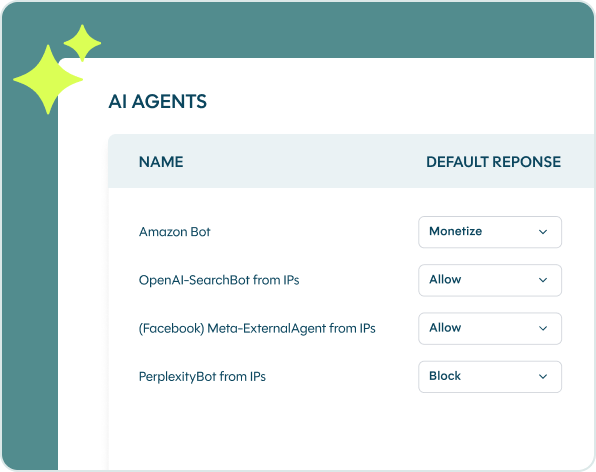
DataDome is the only bot protection solution on the market designed to protect websites, mobile apps, and APIs from Layer 7 DDoS attacks and all other OWASP automated threats. Driven by machine learning models, our algorithm analyzes trillions of signals a day and adjusts in real time across all our customers’ endpoints to detect and block both known bots and new, unfamiliar threats.
DataDome’s Layer 7 DDoS protection solution deploys in minutes on any web infrastructure, with no changes to the host architecture. Layer 7 attack detection and prevention runs on autopilot. DataDome sends you real-time notifications when your site is under an application layer attack, but you won’t need to do anything. Once you have set up an allowlist of trusted partner bots, DataDome takes care of all unwanted traffic.
Are you ready to see which Layer 7 DDoS attacks are targeting your website? Schedule a live demo today.
FAQ's
Layer 3 (network layer) and Layer 7 (application layer) DDoS attacks differ fundamentally in their targeting and efficiency. L3 attacks are volumetric, attempting to overwhelm network bandwidth by flooding it with massive amounts of traffic. L7 attacks are more sophisticated, targeting specific web application functions (like search, login pages, or APIs) that require complex server processing. Since these application functions often need multiple database operations or authentication checks, L7 attacks can bring down a service with significantly less traffic by exhausting server processing power rather than network bandwidth.
Layer 7 DDoS attacks are challenging to detect because they mimic legitimate user behavior. Key detection methods include behavioral analysis to identify abnormal traffic patterns, fingerprinting inconsistencies in HTTP and TLS headers, monitoring for unusual request rates or session patterns, and analyzing contextual signals like IP reputation and geographical distribution. Advanced AI-powered detection systems can identify L7 attacks in under 2 milliseconds by analyzing thousands of signals simultaneously across millions of requests.
The most common Layer 7 DDoS attacks include HTTP flood attacks (sending massive volumes of GET or POST requests), Slowloris attacks (opening multiple connections and sending partial requests to exhaust server resources), DNS query flood attacks (overwhelming DNS servers with queries), and WebSocket connection floods (establishing numerous persistent connections). Modern attackers increasingly use horizontal DDoS attacks, targeting multiple IP addresses and services simultaneously to overwhelm defenses.
| Attack Type | Bandwidth Required | Detection Difficulty | Primary Target | Impact Speed |
|---|---|---|---|---|
| HTTP Flood | High | Medium | Web servers, APIs | Fast (minutes) |
| Slowloris | Very Low | High | Web server connections | Slow (hours) |
| DNS Query Flood | Medium | Medium | DNS infrastructure | Fast (minutes) |
| WebSocket Flood | Low | High | Real-time applications | Medium (30+ min) |
Traditional CDN security and network-layer defenses focus on volumetric attacks and IP reputation, making them less effective against sophisticated Layer 7 attacks. Approximately 20% of traffic passed by CDN security consists of DDoS threats—enough to overwhelm targeted servers. Layer 7 attacks exploit application logic, use encrypted HTTPS traffic that’s difficult to inspect, and employ low bandwidth with high impact tactics that bypass traditional rate limiting. Specialized Layer 7 protection with multi-layered AI detection is required to identify and block these application-layer threats in real time.
Layer 7 DDoS attacks are increasing in duration, with well-orchestrated campaigns often running for several hours, days, or even weeks. Industry research shows attacks lasting longer than 60 minutes continue to increase, as attackers systematically test network defenses before pooling resources to overwhelm bandwidth and connectivity. According to Statista, the number of DDoS attacks jumped from 274,000 in Q1 2023 to 512,000 in Q4 2024, with many of these being sustained, sophisticated campaigns rather than brief incidents.
Yes. Modern Layer 7 DDoS protection solutions integrate seamlessly into existing technology stacks without requiring traffic redirection. DataDome DDoS Protect, for example, offers over 50 out-of-the-box integrations with edge CDNs and server-side platforms including NGINX, F5, HAProxy, and Envoy. This allows organizations to add advanced application-layer defenses to their existing infrastructure without architectural changes, deployment delays, or additional bandwidth requirements.
References
- https://www.statista.com/statistics/1557643/ddos-attacks-global-number/
- https://www.forrester.com/blogs/predictions-2025-cybersecurity-risk-privacy/
- https://www.ibm.com/reports/data-breach
- https://www.forbes.com/sites/chuckbrooks/2025/04/05/key-cybersecurity-challenges-in-2025-trends-and-observations/